Building a Website by Purchasing Your Own ServerThis involves server security issues. Although you may not be aware, your server is being scanned by bots every day. In this article, Naiba shares several Nginx rules that can prevent your server from being scanned.
1. Prohibit Direct Server Access via IP by DefaultEvery server has an IP address, and some bots will directly probe the content on your website by accessing the IP address. We can add the following code in the Nginx configuration to prevent server access via IP address.
#别人如果通过ip或者未知域名访问你的网站的时候,你希望禁止显示任何有效内容,可以给他返回500
server {
listen 80 default;
server_name _;
return 500;
}
#开放一个或多个真实的希望被访问的域名配置,设置如下:
server {
linten 80;
server_name naibabiji.com;
}
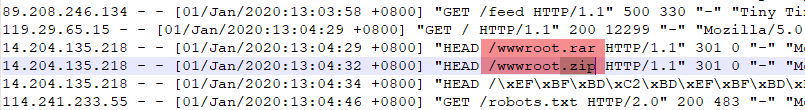
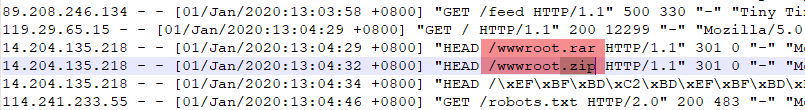
2. Prevent Bots from Scanning Website Compressed FilesSimilarly, many bots will directly access certain files under your domain. For example, the image below shows someone scanning the wwwroot.zip file on Naibabiji.
We can add some 'spice' to it by redirecting links that access these compressed files to a very large file, making them download slowly.
rewrite \.asp/?$ http://speedtest.tele2.net/50GB.zip permanent;
rewrite \.zip/?$ http://speedtest.tele2.net/50GB.zip permanent;
rewrite \.gz/?$ http://speedtest.tele2.net/50GB.zip permanent;
rewrite \.7z/?$ http://speedtest.tele2.net/50GB.zip permanent;
rewrite \.sql/?$ http://speedtest.tele2.net/50GB.zip permanent;
rewrite \.rar/?$ http://speedtest.tele2.net/50GB.zip permanent;
rewrite \.tar/?$ http://speedtest.tele2.net/50GB.zip permanent;The code above means that when accessing files with .asp/zip/gz/7z/sql/rar/tar formats on the website, it automatically redirects to a 50GB zip link. Let them crawl it themselves. We can also give them an even larger file, like 1000GB, to fill up their hard drive.
http://speedtest.tele2.net/1000GB.zip
http://speedtest.tele2.net/100GB.zip
http://speedtest.tele2.net/50GB.zip
Of course, you can also install
Defender Securitythis plugin to help you block these bots. If you don't know how to add redirect rules, you can directly use some plugins that support redirection, such as
RanK Math's redirection feature.
Updated on September 20:Today, it was discovered that new bots are ignoring the above 301 redirects (or is the volume too large?) while scanning the website, causing Naibabiji's server CPU to be maxed out several times. Therefore, another method had to be used. The simplest and most direct method is to add the following rule directly in the nginx configuration, targeting file download links on the server, and directly prohibit access (use with caution for websites that provide local resource downloads).
location ~ \.(zip|rar|sql|bak|gz|7z)$ {
return 444;
}When a user accesses resources like zip, rar, etc., on the website, directly return a 444 error code.
444 No Response Nginx HTTP server extension. The server does not return any information to the client and closes the connection (helps block malware).
There is another method, which is to install a WAF firewall for Nginx. If you are using
Baota Panel, then you can install it directly from the backend software store. If you are using the LNMP one-click installation package, then install it according to the method below. Starting from version 1.5, the LNMP one-click installation package added an option for Lua support. You can enable Lua by changing the parameter after Enable_Nginx_Lua in lnmp.conf to 'y'. If LNMP is not installed, modify lnmp.conf and save it. After installing LNMP, it will support Lua. If LNMP is already installed, also modify lnmp.conf as described above, then run `./upgrade.sh nginx` in the LNMP installation package directory to upgrade Nginx. Enter the current Nginx version number or a newer Nginx version number. After the upgrade is complete, it will support Lua. Installing ngx_lua_waf Download and install ngx_lua_waf:
wget https://github.com/loveshell/ngx_lua_waf/archive/master.zip -O ngx_lua_waf.zip
unzip ngx_lua_waf.zip
mv ngx_lua_waf-master /usr/local/nginx/conf/waf
Set up and enable ngx_lua_waf on Nginx Edit `/usr/local/nginx/conf/nginx.conf`. Add the following code below `server_tokens off;`:
lua_package_path "/usr/local/nginx/conf/waf/?.lua";
lua_shared_dict limit 10m;
init_by_lua_file /usr/local/nginx/conf/waf/init.lua;
Save after modifications. If you want to enable ngx_lua_waf for a specific virtual host, you can modify the server block of the corresponding virtual host. Add the following code below the `root` website directory line in that server block:
access_by_lua_file /usr/local/nginx/conf/waf/waf.lua;
Save after modifications. Test the Nginx configuration file: `/usr/local/nginx/sbin/nginx -t`. Reload the Nginx configuration to take effect: `/usr/local/nginx/sbin/nginx -s reload`. If both the test and reload report no errors, it is already effective. You can test by accessing `http://domain/test.php?id=../etc/passwd`. For more details, you can
Refer to this article。
 We can add some 'spice' to it by redirecting links that access these compressed files to a very large file, making them download slowly.
We can add some 'spice' to it by redirecting links that access these compressed files to a very large file, making them download slowly.
Comments are closed
The comment function for this article is closed. If you have any questions, please feel free to contact us through other channels.